Why You Need Continuous Network Monitoring?
Changes in the way we work have had significant implications for cybersecurity, not least in network monitoring. Workers no longer sit safely side-by-side on a corporate network, dev teams constantly spin up and tear down systems, exposing services to the internet. Keeping track of these users, changes and services is difficult – internet-facing attack surfaces rarely stay the same for long.
But a secure working network is the backbone of every modern business, and with so many different attack vectors and entry points, relying on firewalls and point-in-time scanning is no longer enough. You need to understand how your firewalls are being changed in real-time, with real-world validation of how they’re configured. You need continuous network monitoring.
What needs protecting in your network?#
There is so much sprawl in today’s corporate networks with remote working, cloud computing and third-party integrations, that it’s no longer just the devices or systems that you have in your office and data center that need protecting.
From the hardware and software of the network itself, to all the devices used to access it, from IoT endpoints to laptops and smartphones, network security now needs to look beyond the perimeter to your cloud resources, edge devices, third-party hosted content, integrations with other hardware or software, and assets hosted in dispersed offices.
Just to complicate matters further, some of these services, especially those hosted in the cloud, may only be active for a short space of time for specific projects, events, deployments, or by design. With such a dispersed network, the castle-and-moat model of network security is no longer fit for purpose.
What can go wrong with your network?#
Vulnerabilities can be introduced to your network in a number of ways, including misconfigurations, expiring certificates, new assets added to cloud environments, missing patches, or unnecessarily exposing services to the internet. In addition, there’s the ever-present risk of attack from phishing, supply chain compromises and exposed credentials.
For example, a Windows SMB service on your internal network is not a vulnerability, but exposing one to the internet is a different matter entirely – that’s what led to the WannaCry ransomware attack that spread across the world. Similarly, Australian telco Optus suffered a devastating data breach in 2022 that exposed details of 11 million customers. The breach occurred through an unprotected and publicly-exposed API which didn’t require user authentication, so anyone that discovered the API on the internet could connect to it without a username or password.
How can you protect your network?#
Continuous network monitoring supported by regular scanning could have picked up both of these vulnerabilities and prevented these breaches. Monitoring uses automation to detect and identify flaws and weak spots in your devices, application software and operating systems. It does this by sending probes to look for open ports and services, and once the list of services is discovered, probing each for more information, configuration weaknesses or known vulnerabilities.
It’s common to have a range of systems in your network, from laptops and workstations in the office or at home, to systems in cloud platforms like AWS, Azure, and Google Cloud. Your team may well use a range of operating systems too. Deciding what to include in your network scan can be hard, but there are multiple ways to tackle it: exposure based, sensitivity based and coverage based.
Why do you need to monitor continuously?#
Your network is always changing. New services are spun up, web apps updated, permissions changed, devices added and removed. All of these can introduce potential vulnerabilities. The goal of continuous monitoring is to provide near-immediate feedback and insight into these changes, assessing and prioritizing vulnerabilities, so you can understand the risk across your entire infrastructure.
With this clear picture of what attackers can see and what’s accessible in your internet-facing infrastructure, you can easily tackle any problems as soon as they arise. Continuous monitoring not only provides visibility into the vulnerabilities in your IT environment and remote devices, but also clarity into how those vulnerabilities translate into business risk, and which are most likely to be targeted by attackers.
Continuous network monitoring with Intruder#
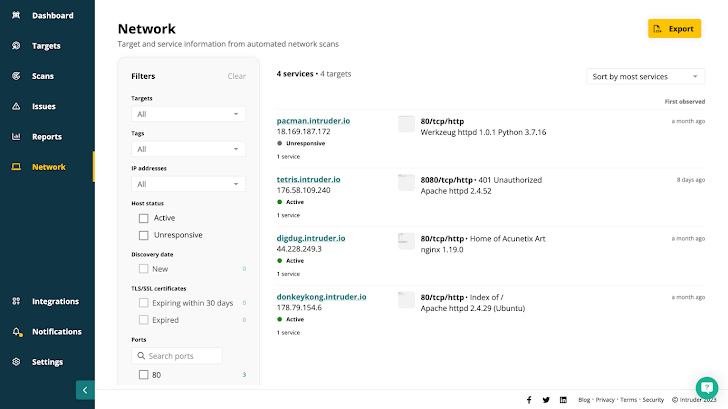
Advanced network monitoring tools like Intruder run daily network scans so your network view is always accurate and up to date – showing active and unresponsive targets, any changes since your last scan, expiring certificates, and the ports and services you expect – and more importantly, don’t expect – to be exposed to the internet.
 |
| Intruder gives you a real view of your attack surface combining continuous network monitoring, automated vulnerability scanning, and proactive threat response in one platform. |
Any targets you add will kick off a scan. Once finished, it adds the target to the queue for rescanning at regular intervals. Any changes will automatically kick off a vulnerability scan, with issues prioritized by context so you can fix what matters most.
If you’re lucky enough to have your own network range, you know how useful it can be but how hard to manage. You want to make sure your whole range is covered, but licensing vast numbers of inactive IPs can be expensive. Intruder monitors your external network ranges for active IPs – but you’ll only pay for the ones in use.
This continuous monitoring gives comprehensive and up-to-date visibility across your entire IT environment to take your network security to another level.
Visit Intruder to activate a free 14-day trial and experience continuous network monitoring for yourself.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.



![[HANDALA] - Ransomware Victim: Hotam EC 3 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)