WordPress fixes POP chain exposing websites to RCE attacks

WordPress has released version 6.4.2 that addresses a remote code execution (RCE) vulnerability that could be chained with another flaw to allow attackers run arbitrary PHP code on the target website.
WordPress is a highly popular open-source content management system (CMS) used for creating and managing websites. It is currently used by more than 800 million sites, accounting for about 45% of all sites on the internet.
The project’s security team discovered a Property Oriented Programming (POP) chain vulnerability that was introduced in WordPress core 6.4, which under certain conditions could allow arbitrary PHP code execution.
A POP chain requires an attacker to control all the properties of a deserialized object, which is possible with PHP’s unserialize() function. A consequence of this is the possibility to hijack the application’s flow by controlling the values sent to megic methods such as ‘_wakeup()‘.
The security issue requires the existence of a PHP object injection flaw on the target site, which could be present on a plugin or theme add-on, to achieve a critical severity.
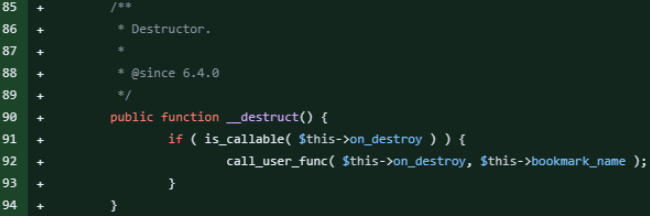
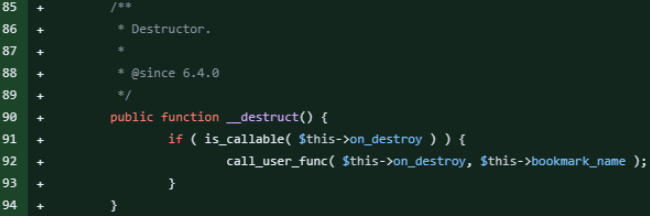
A PSA by WordPress security experts at Wordfence provides some additional technical details on the problem, explaining that the issue is in the ‘WP_HTML_Token’ class, introduced in WordPress 6.4 to improve HTML parsing in the block editor.
The class contained a ‘__destruct‘ magic method, which used ‘call_user_func’ to execute a function defined in the ‘on_destroy’ property, with ‘bookmark_name‘ as an argument.
An attacker exploiting an object injection vulnerability could gain control over these properties to execute arbitrary code, the researchers say.
Although the flaw isn’t critical on its own, due to the need for object injection on installed and active plugins or themes, the presence of an exploitable POP chain in WordPress core significantly increases the overall risk for WordPress sites.
Another notification from Patchstack security platform for WordPress and plugins highlights that an exploit chain for this issue was uploaded several weeks ago on GitHub and later added to the PHPGGC library, which is used in PHP application security testing.
Even if the vulnerability is potentially critical and it is exploitable under certain circumstances, researchers recommend admins update to the latest WordPress version. Even if most updates install the new version automatically, researchers advise checking manually if the update completed.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

