Xenomorph Android malware now steals data from 400 banks

The Xenomorph Android malware has released a new version that adds significant capabilities to conduct malicious attacks, including a new automated transfer system (ATS) framework and the ability to steal credentials for 400 banks.
Xenomorph was first spotted by ThreatFabric in February 2022, which discovered the first version of the banking trojan on the Google Play store, where it amassed over 50,000 downloads.
That first version targeted 56 European banks using injections for overlay attacks and abused Accessibility Services permissions to perform notification interception to steal one-time codes.
Development of the malware continued throughout 2022 by its authors, “Hadoken Security,” but its newer releases were never distributed in high volumes.
Instead, Xenomorph v2, which was released in June 2022, only had short bursts of testing activity in the wild. However, the second version was notable for its complete code overhaul, which made it more modular and flexible.
Xenomorph v3 is far more capable and mature than the previous versions, able to automatically steal data, including credentials, account balances, perform banking transactions, and finalize fund transfers.
“With these new features, Xenomorph is now able to complete automate the whole fraud chain, from infection to funds exfiltration, making it one of the most advanced and dangerous Android Malware trojans in circulation,” warns ThreatFabric.
ThreatFabric reports that it’s likely Hadoken plans to sell Xenomorph to operators via a MaaS (malware as a service) platform, and the launch of a website promoting the new version of the malware strengthens this hypothesis.
Currently, Xenomorph v3 is being distributed via the ‘Zombinder’ platform on the Google Play store, posing as a currency converter and switching to using a Play Protect icon after installing the malicious payload.
New Xenomorph targets
The latest version of Xenomorph targets 400 financial institutions, mainly from the United States, Spain, Turkey, Poland, Australia, Canada, Italy, Portugal, France, Germany, UAE, and India.

Some examples of targeted institutions include Chase, Citibank, American Express, ING, HSBC, Deutsche Bank, Wells Fargo, Amex, Citi, BNP, UniCredit, National Bank of Canada, BBVA, Santander, and Caixa.
The list is too extensive to include here, but ThreatFabric has listed all targeted banks in the appendix of its report.
Moreover, the malware targets 13 cryptocurrency wallets, including Binance, BitPay, KuCoin, Gemini, and Coinbase.
Automatic MFA bypass
The most notable feature introduced in the new Xenomorph version is the ATS framework, which enables cybercriminals to extract credentials automatically, check account balances, conduct transactions, and steal money from target apps without performing remote actions.
Instead, the operator simply sends JSON scripts which Xenomorph converts into a list of operations and executes them autonomously on the infected device.
“The [ATS execution] engine used by Xenomorph stands out from its competition thanks to the extensive selection of possible actions that are programmable and can be included in ATS scripts, in addition to a system that allows for conditional execution and action prioritization,” explains ThreatFabrics researchers.
One of the most impressive capabilities of the malware’s ATS framework is its ability to log the content of third-party authentication applications, beating MFA (multi-factor authentication) protections that would otherwise block automated transactions.
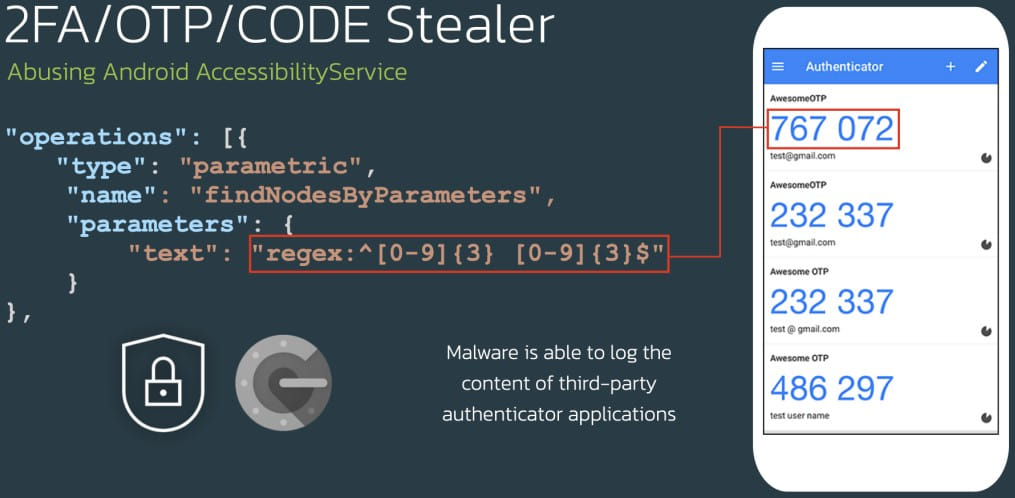
Banks are gradually abandoning SMS MFA and instead suggest that customers use authenticator apps, so seeing Xenomorph’s ability to access these apps on the same device is disturbing.
Cookies stealer
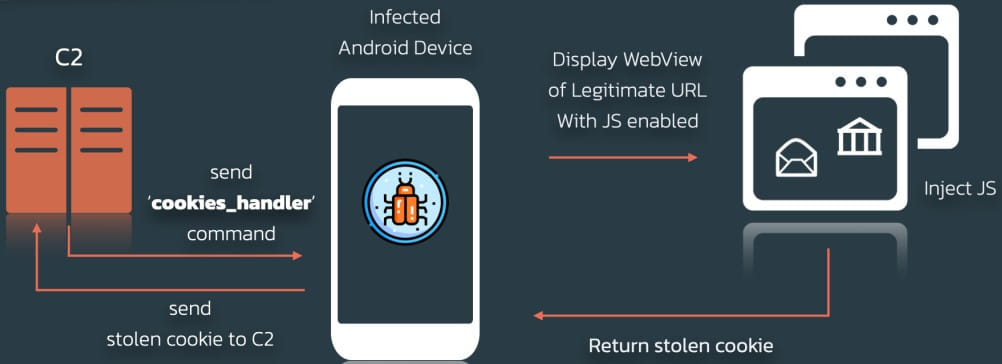
In addition to the above, the new Xenomorph features a cookies stealer that can snatch cookies from the Android CookieManager, which stores the user’s session cookies.
The stealer launches a browser window with the URL of a legitimate service with the JavaScript interface enabled, tricking the victim into entering their login details.
The threat actors steal the cookie, which makes it possible to hijack the victim’s web sessions and take over their accounts.
An Android malware to be worried about
Xenomorph was a notable new malware entering the cybercrime space a year ago.
Now, with the release of its third major version, it is a far greater threat to Android users worldwide.
Considering its current distribution channel, the Zombinder, users should be cautious with apps they install from Google Play, read reviews, and run background checks on the publisher.
Generally, it is advisable to keep the number of apps running on your phone to the minimum possible and only install apps from known and trustworthy vendors.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below


To keep up to date follow us on the below channels.






