Bizarro: a banking Trojan full of nasty tricks
Researchers have discovered a new banking Trojan that has been found targeting customers of European and South American banks. They have dubbed the new Trojan Bizarro.
How does Bizarro spread?
The Bizarro malware spreads via Microsoft Installer (MSI) packages. Identified sources so far have been spam emails and attackers may also use social engineering to convince victims to download a smartphone app. Experts have detected infections in Brazil, Argentina, Chile, Germany, Spain, Portugal, France, and Italy. Bizarro uses compromised WordPress, Amazon, and Azure servers to host the MSI packages that victims are tricked into downloading.
What is Bizarro capable of?
Bizarro has quite a few tricks up its sleeve:
- It can capture login credentials entered on banking sites. To speed up this process it reportedly closes your existing browser windows, so you are forced to log in. Bizarro also creates fake prompts to solicit 2FA codes.
- Bizarro constantly monitors the clipboard and will replace any Bitcoin address it finds there with its own (hoping of course to capture any transfers that were supposed to be paid into the original address).
- And last, but not least, it is a full-blown backdoor, which gets fired up as soon as the user visits one of a set of hardcoded banking sites.
The backdoor offers a lot of options to the attacker, including:
- Gathering data about the infected system and sending them to the C&C server.
- Searching for and stealing files from the infected computer.
- Dropping files on the affected system (such as other malware).
- Remote control of the mouse and keyboard.
- Keylogging.
- Creating fake popup windows and messages. The messages are intended to slow down the user’s response time and include progress bars.
- Emulating banking sites on the fly.
Targets
Like many other banking Trojans of Brazilian origin, Bizarro focuses on European and South American banks. Attempts have now been made to steal credentials from customers of 70 banks from different European and South American countries.
Besides the obvious victims that get the malware on their system, Bizarro also use money mules to operationalize their attacks, cash out, or simply to help with transfers. These money mules often have short-lived criminal careers before they end up in jail.
Mitigation and detection
As always the most important advice is to not click on links that come from an uncertain source. Also keep an eye out for unexpected behavior on your system. Especially when it comes to banking, it’s better to look into weird behavior than to just assume it’s Windows acting up. And double check your destination bitcoin addresses before sending them funds. (This is good advice in all circumstances: This isn’t the only malware that uses the clipboard to replace bitcoin addresses, and there are no do-overs with bitcoin!)
The downloaded ZIP archive contains the following files:
- A malicious DLL written in Delphi
- A legitimate executable that is an AutoHotkey script runner (in some samples AutoIt is used instead of AutoHotkey)
- A small script that calls an exported function from the malicious DLL
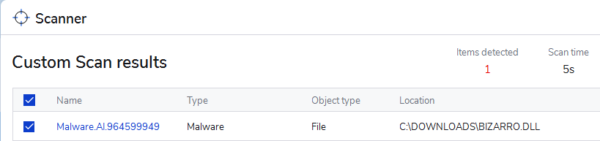
The DLL is detected by Malwarebytes’ machine learning module.
Stay safe, everyone!
The post Bizarro: a banking Trojan full of nasty tricks appeared first on Malwarebytes Labs.
If you like the site, please consider joining the telegram channel or supporting us on Patreon using the button below.



