Critical Security Vulnerability Patched By VMware
VMware Inc. a publicly-traded software company recently fixed a critical security vulnerability that permitted the malicious attackers to access sensitive data.
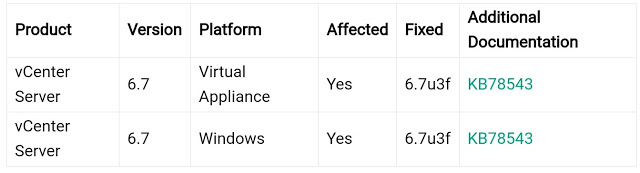
The vulnerability as indicated by them resides in the VMware Directory Service (vmdir) which is a part of vCenter Server version 6.7 on Windows and virtual appliances. Known and tracked as CVE-2020-3952, it is evaluated as critical and gets a CVSSv3 score of 10.
In certain conditions, the vmdir doesn’t actualize appropriate security controls, which permits attackers with network access to get to the sensitive data.
By utilizing the obtained information the attacker can compromise vCenter Server or various other services that rely upon vmdir for authentication.
In March VMware tended to high severity privilege escalation and DoS in the Workstation, Fusion, VMware Remote Console and Horizon Client and furthermore published KB article 78543 for additional details if a vCenter Server 6.7 deployment is influenced in any way.
It is recommended for the user on the off chance that they are utilizing vCenter Server version 6.7, to update with 6.7u3f to fix the aforementioned critical vulnerability.
Here is the example log to check with influenced deployments.
2020-04-06T17:50:41.860526+00:00 data vmdird t@139910871058176: leg tendon MODE: Heritage
VMware lastly mentioned that “Clean installations of vCenter Server 6.7 (embedded or external PSC) are not affected.”


