IBM’s X-Force says who needs malware, PowerShell FTW!
If anyone reading this works in InfoSec, as I do then you will know that a company’s internal network, once compromised, is now more likely to be ransacked by automated scripts using tools already on the network and white-listed than a piece of malware.
Please follow me on:
Twitter
 Telegram
Telegram

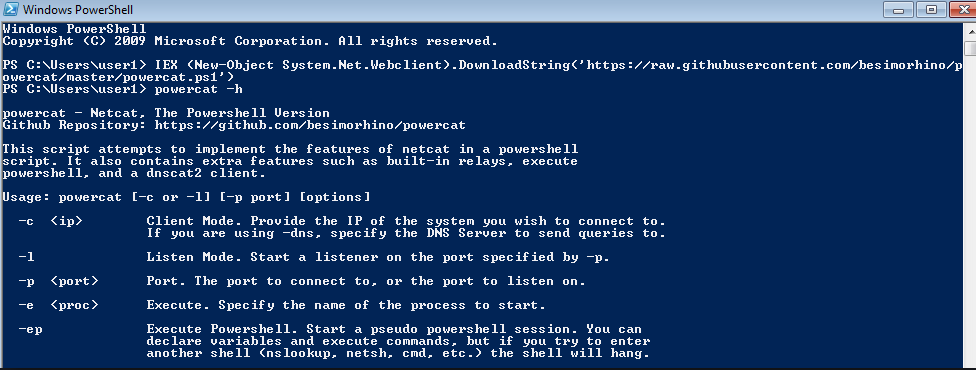
This according to researchers with IBM’s X-Force, who found that in 2018 just 43 per cent of the attacks it analysed utilised any sort of locally installed files. Rather, the hackers utilised PowerShell scripts to execute their dirty deeds in memory without significantly touching file systems, if at all.
This finding is important because it is another reminder that admins can no longer solely rely on detecting malicious executable’s and similar data on hard drives and other storage, to identify cyber-intrusions.
As with local malware infections, the attacker first needs to get the ability to run malicious commands. What differs is the next step, as the miscreant does not direct the infected Windows machine to download, save, and execute a trojan payload.
Rather, the attack runs entirely in memory using PowerShell, where Microsoft’s powerful scripting language can be used to do anything from harvest and steal passwords to mine cryptocurrency. It is possible to wrap protections around PowerShell to stop it being abused, such as requiring scripts to be digitally signed.
“PowerShell is useful in data collection and analysis, but it is also favoured by malicious actors who use it to forego the file system and inject malicious code directly into memory, thus enhancing obfuscation, and often evading security controls designed to detect malware deployments, threat actors of all skill levels have expanded their capabilities using PowerShell over the last few years. IBM X-Force IRIS has seen cases wherein complete malicious tool-kits were contained within PowerShell scripts.”
the IBM report reads.
In some cases, crooks wouldn’t even need to run a l33t exploit to steal corporate data. The X-Force report notes that misconfiguration incidents – instances where databases and storage buckets were left exposed to the public-facing internet – were also up 20 per cent from last year and accounted for 43 per cent of all of the exposed records X-Force tracked last year.
In addition to the exposed files and records themselves, misconfigurations could also indirectly lead to other attacks when things like passwords and email addresses are involved and used to login to other accounts on other services to carry out further mischief.
Finally, the report found, the tried and true social engineering attack remains as effective as it has ever been.
Last year, IBM found that 29 per cent of the attacks it analysed were phishing attacks, and 45 per cent of those were targeted attacks on specific employees, something X-Force terms the business email compromise.
“When it comes to the most lucrative types of social engineering scams, BEC has been a growing tide for several years spanning all industries and geographies,” notes X-Force.
It seems that, despite the various methods for sophisticated attacks, a bogus “CEO” email demanding a wire transfer is still a foolproof way to con a company out of cash.

![[INTERLOCK] - Ransomware Victim: City of Peabody, MA 4 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)

