PCI DSS compliance: why it’s important and how to adhere
PCI DSS is short for Payment Card Industry Data Security Standard. Every party involved in accepting credit card payments is expected to comply with the PCI DSS. The PCI Standard is mandated by the card brands, but administered by the Payment Card Industry Security Standards Council (PCI SSC). The standard was created to increase controls around cardholder data to reduce credit card fraud.
The PCI Security Standards Council’s mission is to enhance global payment account data security by developing standards and supporting services that drive education, awareness, and effective implementation by stakeholders.
Compliance will ensure that a company can uphold a positive image and build consumer trust. This also helps build consumer loyalty, since customers are more likely to return to a service or product from a company they consider to be trustworthy.
What exactly is PCI DSS?
PCI DSS is an international security standard that was developed in cooperation between several credit card companies. The PCI DSS tells companies how to keep their card and transaction data safe.
When the PCI DSS was published in 2004, it was expected that organizations would achieve effective and sustainable compliance within about five years. Some 15 years later, less than half of organizations maintain programs that prevent PCI DSS security controls from falling out of place within a few months after formal compliance validation. According to a 2019 Verizon Payment Security Report, research shows that PCI sustainability is trending downward since 2017.
An increase in online transactions
One of the side effects of the COVID-19 pandemic has been an increase in online transactions. As more people worldwide have started to work from home and practice social distancing to combat the spread of COVID-19, businesses must prepare to handle a higher percentage of online transactions.
After all, it is likely that these online customers will continue to shop online when they learn to appreciate the ease of use, especially if they are confident about the security of their online transactions. However, with this rise in the frequency of digital payments comes the increased threat of data breaches and digital fraud.
The elements of compliance
A recent Bank of America report states that small businesses are protecting themselves by implementing industry security standards, like PCI compliance. Specifically, PCI Compliance Requirement 5 indicates that you must protect all systems against malware and regularly update anti-malware software. PCI DSS Requirement 5 has four distinct elements that imply they need to be addressed daily:
- 5.1: For a sample of system components, including all operating system types commonly affected by malicious software, verify that anti-malware software is deployed.
- 5.2.b: Examine anti-malware configurations, including the master installation of the software, to verify anti-malware mechanisms are configured to perform automatic updates and periodic scans.
- 5.2.d: Examine anti-malware configurations, including the master installation of the software and a sample of system components, to verify that the anti-malware’s software log generation is enabled, and logs are retained per PCI DSS Requirement 10.7.
- 5.3.b: Examine anti-malware configurations, including the master installation of the software and a sample of system components, to verify that the anti-malware software cannot be disabled or altered by users.
Basically, this boils down to our regular advice pillars:
- Make sure software (including anti-malware) is updated.
- Perform automatic and/or periodic scans for malware.
- Log and retain the results of those scans.
- Make sure protection software (especially anti-malware) can’t be disabled.
Common problems and objections
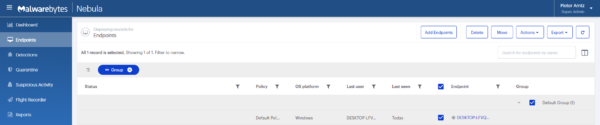
The first requirement (5.1) requires an organization to maintain an accurate inventory of their devices and the operating systems on those devices. However, configuration management database (CMDB) solutions are notorious for not being completely implemented. As a result, it can be quite an exercise to determine if every system that needs anti-malware software is installed. If so, look for a solution that provides an inventory of protected endpoints for you. You may use such an inventory for auditing your CMDB and verifying compliance.
The next hurdle with requirement 5.1 is that we still run into pushback from macOS and Linux users/administrators over their need to run an antivirus solution. Yet, a review of the CVE database debunks those claims.
Yes, these OSes have fewer vulnerabilities than Windows. However, they would still be “commonly affected,” given the number of vulnerabilities and the frequency with which those vulnerabilities are published. And as we have reported in the past, Mac threat detections are on the rise and actually outpace Windows in sheer volume. Using a solution that can cover all the operating systems in use in your organization can help you organize and control all your devices without adding extra software.
Sometimes, you will get pushback from server administrators who swear that any antivirus solution takes too much CPU to run and adversely affects server performance. While it’s getting better, we still regularly encounter people who make this claim but then fail to provide documented proof. (Not that we don’t believe them, as there are several legacy antivirus programs that can adversely affect performance.)
However, in most cases, the person is making these claims based on past experiences and not on trials of a more contemporary solution. No matter how you look at this, you will have to deploy anti-malware on Windows, macOS, and Linux Server endpoints to meet the PCI DSS.
Why compliance matters
Data from the Verizon Threat Research Advisory Center (VTRAC) demonstrates that a compliance program without the proper controls to protect data has a more than 95 percent probability of not being sustainable and is more likely to be the potential target of a cyberattack.
The costs of a successful cyberattack are not limited to liabilities and loss of reputation. There are also repairs to be made and reorganizations may be necessary, especially when you are dealing with ransomware or a data breach.
A data breach also involves lost opportunities and competitive disadvantages that are near impossible to quantify. The 2019 IBM/Ponemon Institute study calculated the cost of a data breach at $242 per stolen record, and more than $8 million for an average breach in the US. Ransomware is the biggest financial threat of all cyberattacks, causing an estimated $ 7.5 billion in damage in 2019 for the US alone.
For those companies engaged in online transactions, reputational damage can be fatal. Imagine customers shying away from the payment portal as soon as they spot your logo. PCI compliance, then, is not just a regulation—it could quite literally save your company’s bacon.
So stay safe (which in this case means staying compliant)!
The post PCI DSS compliance: why it’s important and how to adhere appeared first on Malwarebytes Labs.
If you like the site, please consider joining the telegram channel or supporting us on Patreon using the button below.


![[INCRANSOM] - Ransomware Victim: CF Construction Ltd 3 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)

